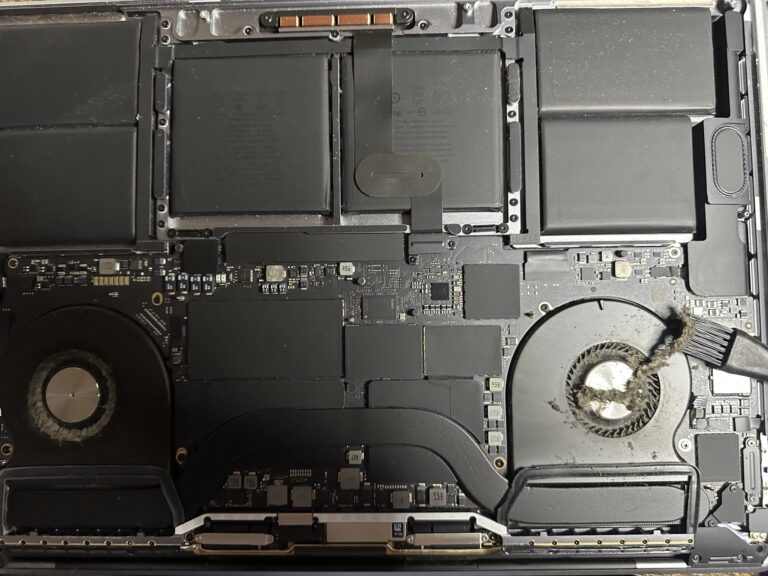
If you’ve been following my journey, you might know that I recently bought an M2 Max MacBook Pro. However, I also own a 2019 Intel MacBook Pro, which started to slow down significantly in recent days. Thankfully, I was able [Read More…]
IETF 108 Hackathon – online
Quick and straight forward presentation at the IETF hackathon 108 which was online throughout the world. I was together with the cyberstorm.mu team though the time difference, I was able to collaborate with Logan to make it a success. On [Read More…]