The last cyberstorm.mu event was on OpenSource licensing with Dr. Till Jaeger at Flying Dodo, Bagatelle Mall Mauritius. We discussed several issues concerning cybersecurity laws, trademarks, OpenSource licensing issues etc.. Dr. Till Jaeger appreciated the meetup and encouraged us to evangelize more on OpenSource. The event was organized by Loganaden Velvindron member of cyberstorm.mu.
[caption id="attachment_2987" align="aligncenter" width="707"]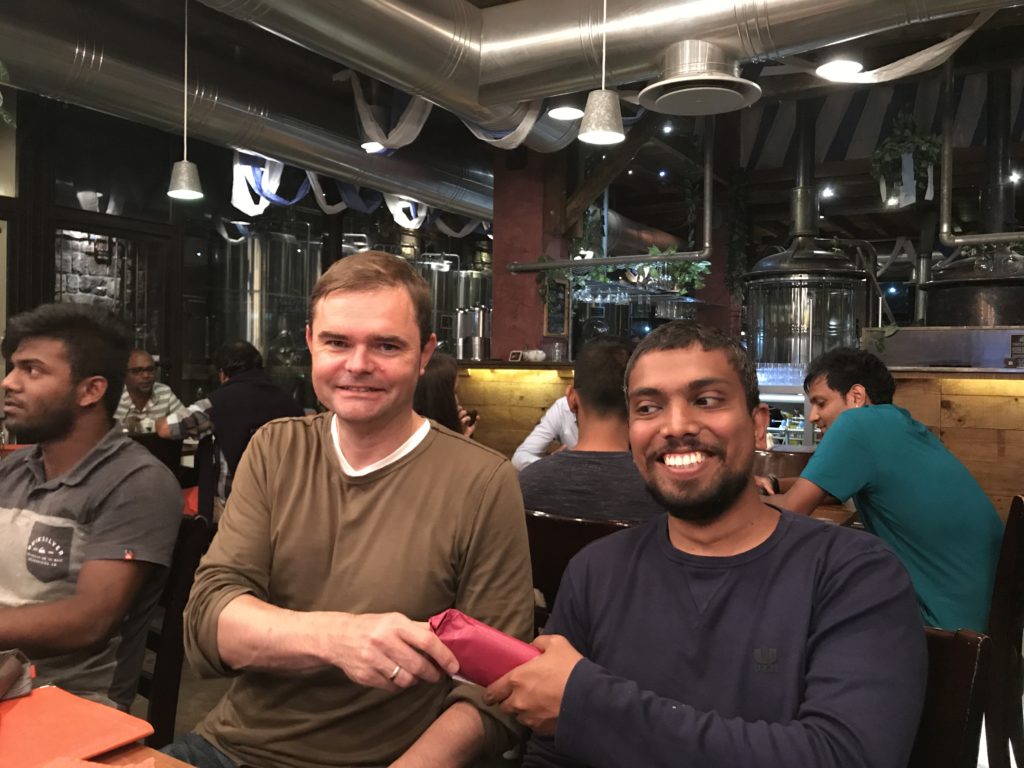
I should say that we were already planning about our next event, hence, a hackathon on Operation KSK-ROLL by the cyberstorm.mu team which was pretty easy, important and successful. Dr. Till Jaeger congratulate us for creating the cyberstorm.mu team. Several pull requests sent to many repositories to encourage developers to adopt the new key.
What is Operation KSK-ROLL?
At cyberstorm.mu all Non-IETF hackathons are usually given a name. This time for the KSK rollover hackathon we have chosen 'Operation KSK-Roll'. Operation KSK-ROLL has been started to make sure that software is up-to-date with the new KSK key.
What is the KSK rollover?
The DNS KSK Rollover happened on 11 October at 11:00 UTC. Rolling the KSK means generating a new key cryptographic key pair (public and private key).
What are those keys?
The public key is distributed to those who operate valid DNS resolvers such as ISPs, network administrators, system integrators etc.. whilst, the private key is kept secret.
If its secret, why do we need to generate another secret key?
For security purpose, the secret key is generated anew and this ensures that DNS resolvers have a more robust security layer on top of the DNS AKA: DNSSEC
What are DNS resolvers?
All websites, example tunnelix.com which is a domain name is behind an IP Address. For your browser to be able to resolve the website, a DNS resolver which is located at several parts of the world will identify the IP with the domain name. Consequently, this will render the website on your browser.
What is DNSSEC?
As mentioned previously, DNSSEC (DNS Security) is a layer added by ICANN to ensure by means of cryptographic keys to ensure an online protection from the provider of the root domain name to your browser.
How will you know if a website is DNSSEC signed?
There is a tool by VeriSign lab which provides DNSSEC Analyzer. You can enter the name of the domain, say tunnelix.com which will analyze the domain show you the public key and the chain from the . (dot), com and tunnelix.com.
[caption id="attachment_3005" align="aligncenter" width="435"]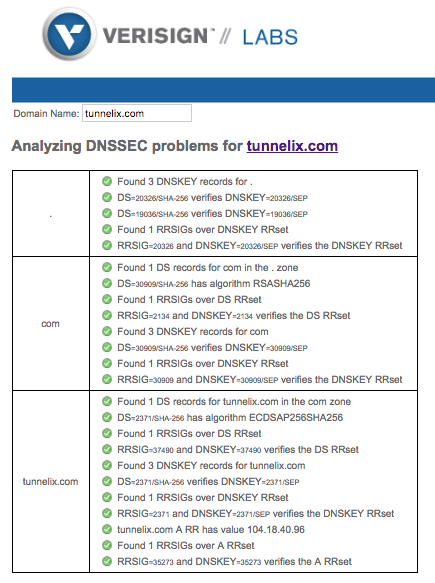
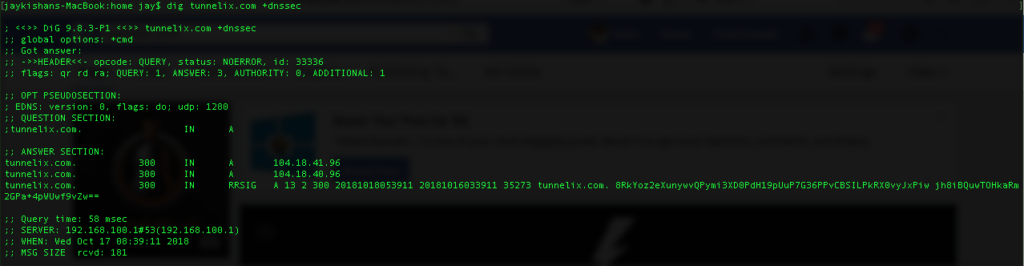
Is there another way to verify it?
Yes, you can use the nslookup or dig tool to check it. In the case of the dig tool here is a screenshot.
What is the logic behind the DIG command?
Some years back (the Year 2015), I explained the anatomy of the dig command. You can view more details about the blog post called "Anatomy of a simple dig result".
What is the role of the KSK?
The KSK private key is used to generate a digital signature for the ZSK. In fact, the KSK public key is stored in the DNS to be used for authenticating the ZSK. So, the KSK is a key to sign another key for the ZSK. That is why it is called the "Key Signing Key".
So, what is the ZSK?
The ZSK (Zone Signing Key) is another private-public key pair which is used to generate a digital signature known as RRSIG ( Resource Record Signature). The RRSIG in itself is a digital signature for each RRSET (Resource Record Sets) in a zone. In fact, the ZSK is stored in the domain name system to authenticate the RRset.
What are RRsets?
RRsets (Resource Record sets) is a group of records DNS Record Set (RRsets) with the same record type, for example, all DNS A records are one RRset.
My contributions for KSK ROLL Please follow me on my GitHub account. One of the repositories is Nagval which is a plugin to check the validity of one of more DNSSEC domains. For more information about DNSSEC, ZSK, PSK etc, I would advise to check out Cloudflare which provided a good source of information.Cyberstorm.mu continue to go beyond and further with innovations and more ideas to protect and secure the Internet. We believe that though we are a small team will be able to recruit more people who are strongly interested in developing their skills to strive for excellence.
I also wish to seize this opportunity to thanks Manuv Panchoo for designing the logo of tunnelix.com
[caption id="attachment_3001" align="alignnone" width="960"]