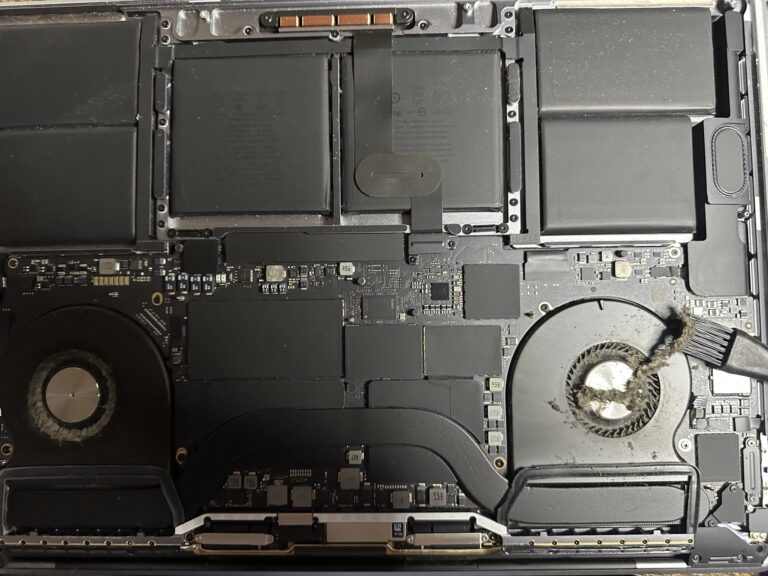
If you’ve been following my journey, you might know that I recently bought an M2 Max MacBook Pro. However, I also own a 2019 Intel MacBook Pro, which started to slow down significantly in recent days. Thankfully, I was able [Read More…]
How i optimised my WordPress website ?
Some days back, I was brewing up some plans to optimize my website source codes, HTTP headers, latency, and other security aspects. I had to carry out some analysis and research using some tools available on the internet. I should [Read More…]