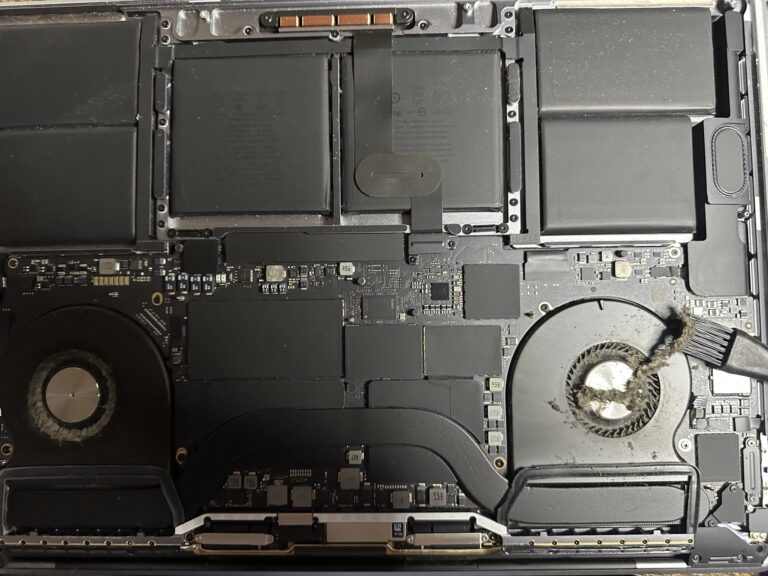
If you’ve been following my journey, you might know that I recently bought an M2 Max MacBook Pro. However, I also own a 2019 Intel MacBook Pro, which started to slow down significantly in recent days. Thankfully, I was able [Read More…]
Operation JASK – Just a Single Keystroke
Apart from the IETF hackathons, the cyberstorm.mu team also focused on internal hackathon either remotely or on-site participation. Another remote hackathon was already in progress since Saturday the 16th of June 2018. It was named Operation JASK – Just a [Read More…]