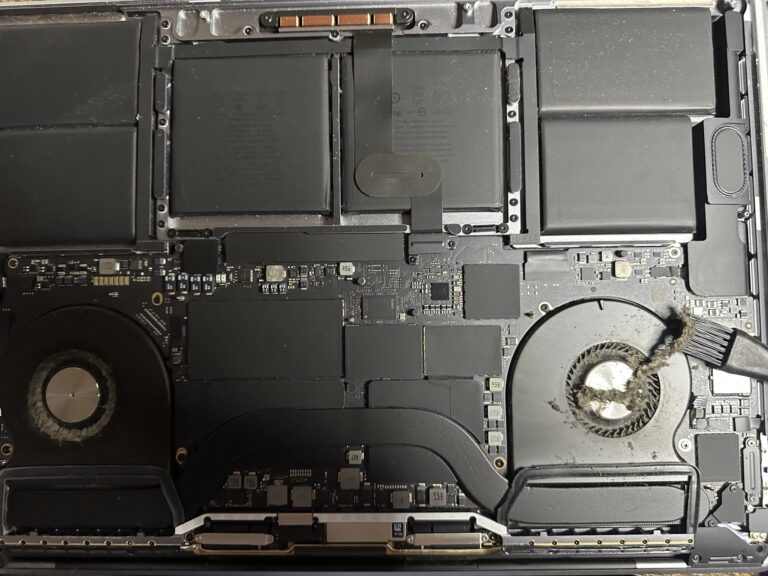
If you’ve been following my journey, you might know that I recently bought an M2 Max MacBook Pro. However, I also own a 2019 Intel MacBook Pro, which started to slow down significantly in recent days. Thankfully, I was able [Read More…]
Solace Certified Solutions Consultant – Learn and get certified
I finally did the certification yesterday and got certified as Solace Certified Solutions Consultant. Some days back, the CEO of my current job asked for a challenge to whoever is the first to complete that exam will win 1000 USD. [Read More…]