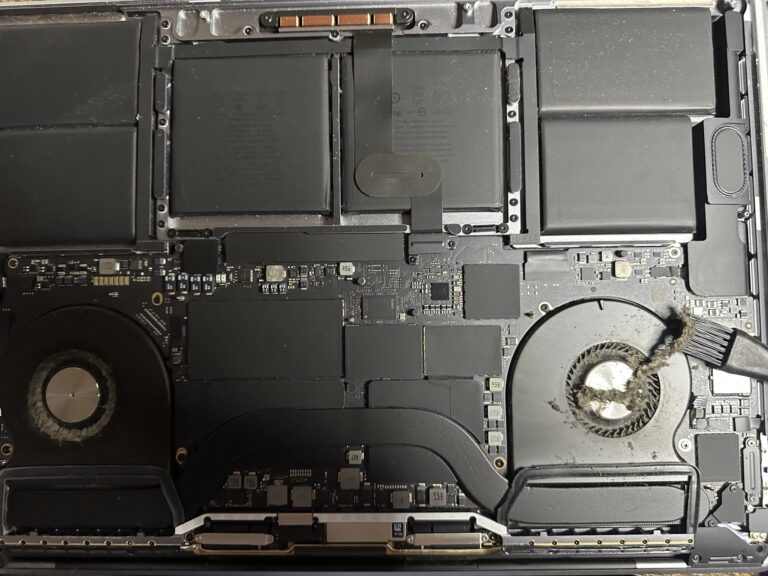
If you’ve been following my journey, you might know that I recently bought an M2 Max MacBook Pro. However, I also own a 2019 Intel MacBook Pro, which started to slow down significantly in recent days. Thankfully, I was able [Read More…]
IETF 100 hackathon on TLS 1.3 by cyberstorm.mu
Some days back, The Register mentioned cyberstorm.mu (name rebranded due to trademark issues) preparing for IETF100 hackathon. Hooray! Yeah, we did it and the hard work finally paid off thanks to the core team and the whole of cyberstorm.mu team. [Read More…]