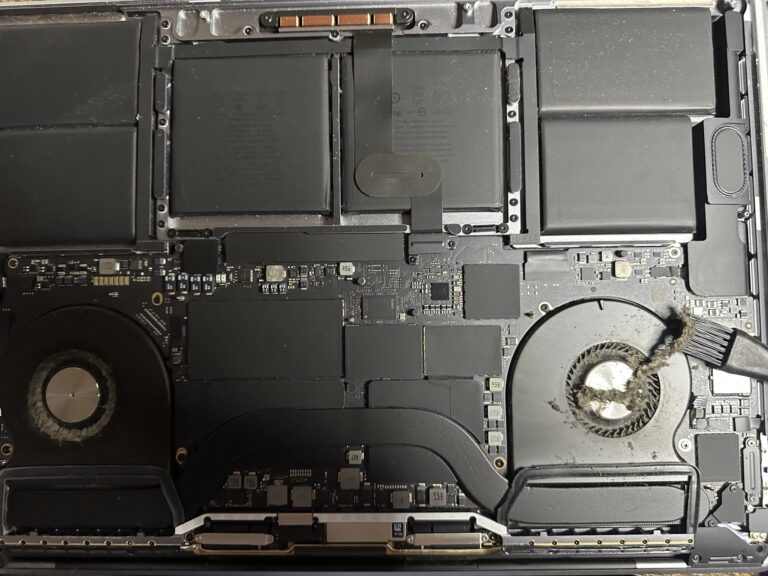
If you’ve been following my journey, you might know that I recently bought an M2 Max MacBook Pro. However, I also own a 2019 Intel MacBook Pro, which started to slow down significantly in recent days. Thankfully, I was able [Read More…]
Cybersecurity Event in Mauritius
International cybersecurity expert Philipp Buehler is coming to Mauritius. He will be speaking about his experience in security and what recommendations he has for people who want to get into the field or just wants to learn new skills in that [Read More…]