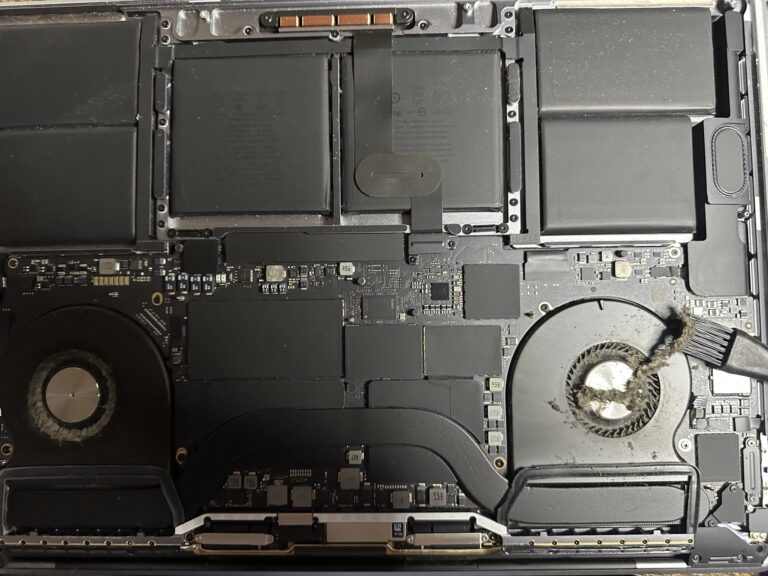
If you’ve been following my journey, you might know that I recently bought an M2 Max MacBook Pro. However, I also own a 2019 Intel MacBook Pro, which started to slow down significantly in recent days. Thankfully, I was able [Read More…]
Some tips with Ansible Modules for managing OS and Application
In the year 2016, I published some articles on Ansible: Getting started with Ansible deployment, which provide some guides to get started with Ansible, setting up the SSH key and other basic stuffs. Another article is about LVM configuration on [Read More…]