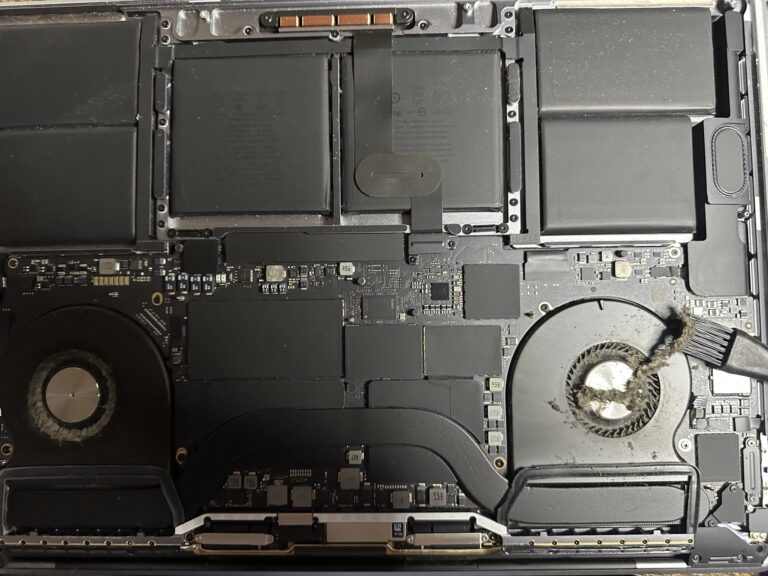
If you’ve been following my journey, you might know that I recently bought an M2 Max MacBook Pro. However, I also own a 2019 Intel MacBook Pro, which started to slow down significantly in recent days. Thankfully, I was able [Read More…]
Introducing MariaDB MaxScale 2.0 – Webinar
Today, I attended a webinar conference on MariaDB MaxScale carried out by Roger Bodamer at 10.00 AM PDT. That was really interesting and I strongly feel the future of system and database administrators are going to be enhanced with this technology. [Read More…]